Hi There,
For this test I’m going to use windows 7 although I have tested on server 2012 rc2 and the result was the same. I also tested the PC version with a user who just locks their desktop.
If your going to test this on windows 7 or 10 you may need to make changes to termsrv.dll file to allow more then one user to connect via rdp.
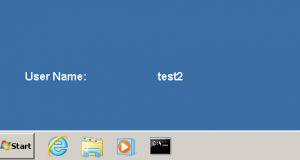
We are connected to the PC via RDP with the account test (rdp-tcp#0) test2 is a disconnected session with the ID 1 and this is the account we want to take over.

To take over the disconnected session you need to run the command under the system account to achieve this for testing this you can create a service although there are other methods to test this but basically anyway you can get a system account.

The syntax on tscon can be found here obviously don’t enter a password.
OK lets run the service and see what we get.

We are then connected to the disconnected session depending on your settings such as “end disconnected session timings” remote desktop users tend to just disconnect their sessions thinking they are logging out.
Don’t forget to clean up afterwards. I found with the pc hijack if the user came back to unlock their PC it would show you connected even if you had logged out by end tasking remotely logonUI.exe would refresh the screen.
